The 2022 Nobel Prize in Physics was awarded to three scientists “for experiments with entangled photons, establishing the violations of Bell Inequalities and pioneering quantum information science”. The press release dated October 04, 2022, noted that “the ineffable effects of quantum mechanics are starting to find applications and that the one very factor is how quantum mechanics allow two or more particles to exist in an entangled state and what happens to one of the particles of an entangled pair determines what happens to the other particle, even if they are far apart.
Quantum Technology
Quantum technology is any class of technology new or old that works by using the principles of quantum mechanics. Quantum technology revolutionises the concept of information processing from the earlier mechanical to digital mode a step further. It uses the dynamics of quantum physics or the behaviour of the universe’s smallest particles, the atom and the behaviour of matter at the sub-atomic scale. Quantum phenomenon is not new but was the basis of development of lasers and semi-conductors since the 1950s. Emerging quantum information technologies will lead to development of quantum computers, radars, cryptography and other systems by utilising the principles of quantum physics. At the very basic level, the technologies use the quantum principles of “entanglement” and “superposition” to share information by ways that are not possible in the classic electronic computers.
Superposition
Superposition is a term to describe the ability of any particle to exist across many states at the same time until it is measured so a particle is said to be in a “superposition” of all those possible states. Superposition has an implication on the concept of computing. Today’s computing involves information in bits; either zero or one. Quantum computers would process information in quantum bits or qubits which can be one, zero or a superposition of the two states which is huge number of possible states making computation exponentially faster than the most advanced available traditional computers today. In a coin analogy a bit is like a tossed coin which lands either as a head or tail. Qubit is like a spinning coin, it can either be head or tail or numerous possibilities in between or neither.
Entanglement
Entanglement is a situation when two or more particles are in the same quantum states and cannot be described independently even if they are separated by large distances and can be thought of being part of the same system. It is like flipping a coin in two different cities at the same time and they being in the same state. When used in technology it reduces the number of logic operations to solve complex problems in quantum computers. Observing a quantum system or measuring it results in the collapse of the system. A spinning coin when flapped leads to it falling either as a head or tail and the system is not then in the quantum state. There are enormous challenges in developing a quantum computing systems which is now possible in strict laboratory conditions under extreme low temperatures.
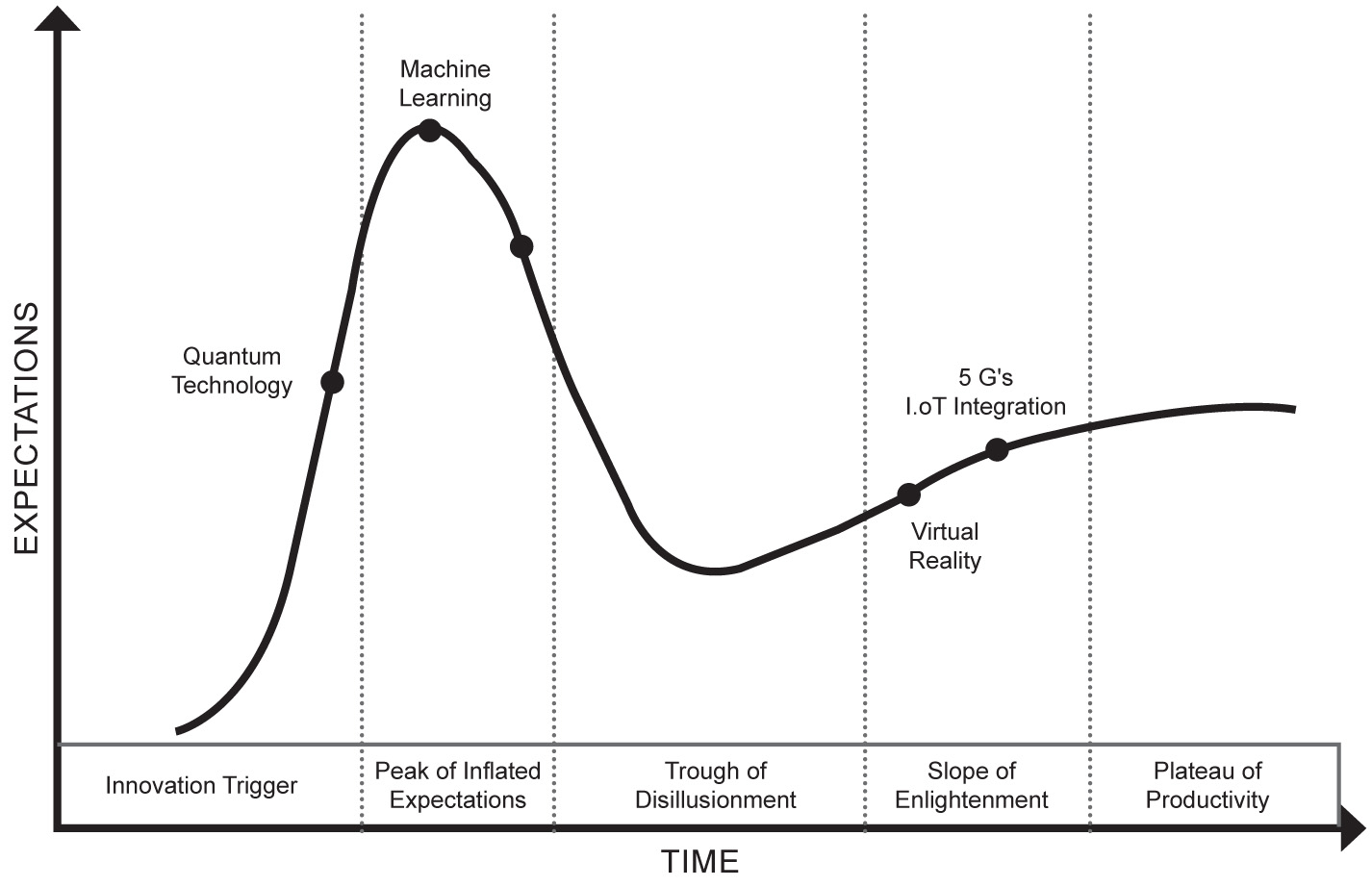
Gartner’s Hype Cycle and the Blind Spot for Security Planners
The Gartner curve depicts the concept of technology hype. It has two parts, the expectations and visibility (Bell curve) and the diffusion or adaption phase (S curve). Based on a time scale, it has five phases. Innovation Trigger, Peak of Inflated Expectation, Trough of Disillusionment, Scope of Enlightenment and Plateau of Productivity. It is not a perfect concept but provides a useful insight of technology evolvement over time for policy makers. Technology is routinely studied in business and science fields ‘scientifically’ but rarely done so in security related matters. Acceptance of a threat in security, both military and intelligence fields would depend on the acquaintance with the threat the technology poses. Non-familiarity would either lead the threat to be underplayed (“caught by surprise”) or overplayed and a disproportional allocation of resources. Therefore, inaccurate assessment of technology would lead to a distorted threat perception or analysis.
Technology hype is, therefore, in extricable linked to National Security. The problem is that emerging technologies are difficult to assess and the gap between expectations and real delivery can be an arduous task to calculate especially when they fall in the rising part of the bell curve which may turn out to be a “blind spot” for security planners. Any strategy formulation can be by way of a disinterested analysis making agenda setting and resource allocation difficult.
One early example of acceptance of technology hype critical to national security was the Einstein’s letter to Roosevelt about the possibility of an atomic bomb in 1939, which led to the Project Manhattan, and ultimately, to the Hiroshima bomb. A contrary example of threat inflation due to technology hype was the miscalculation of the WMD threat and the war on Iraq. Since Quantum technology offers both opportunities and threat to the National Security and falls in the ‘blind spot’ for Policy Making on the Garner’s hype cycle a dispassionate discussion become imperative.
Quantum Technology and National Security
In the year, 2019, Google claimed to have done some calculations using quantum computer within 200 seconds which, at that time, the most advanced super computer could have taken 10,000 years. In the year, 2020, China’s Jiuzhang claimed to have calculated ten billion times faster than Google’s sycamore computing system. “Jiuzhang 2” can compute calculations at least 100 trillion times faster than Google Sycamore!! The potential of quantum computing has extraordinary potential for both economic growth and national security, a reason enough to be watchful.
In 2018, China developed a radar using the principles of quantum physics which could detect stealth aircraft by “unstealthing” them. Other applications of this technology could be to enhance battlefield communication and make submarine navigation undetectable. Quantum radars use entangled pair of photons, which help detect even the faintest of return signals. China’s claim of detecting objects 100km away may be doubtful but its prototype could be a technology demonstrator.
China’s other claim was that by using Quantum Key Distribution (QKD) qubits satellites can send encrypted messages between location as far as Shanghai and Beijing. If enemies try to intercept, the delicate quantum state is destroyed, messages are wiped out and intrusion can be suspected. Countries are working on quantum teleportation system to make them more robust. Navigation tools using quantum sensing are also being developed for areas devoid of GPS system or during enemy spoofing of the GPS System. Quantum compass that use microscopic synthetic diamonds have atomic flaws called Nitrogen Vacancy (NV) centers. They may also be used to spot submarines at longer ranges. Just as in the past, code-shattering had been a vital ingredient in changing the course of World War II, quantum encryption and radars could be the disruptive technologies of the future. This has application in chemical and biological warfare weapons development and use. Quantum simulation can help speed-up development of such weapons and aid in detection in the use of chemical agents. Although all fields are in the realm of various stages of development no country would like to be caught by a “quantum surprise”.
Quantum Communications
Quantum principles can be utilised for secure communications through quantum cryptography. One approach is the quantum key distribution (QKD) where if an adversary tries to intercept and read the key the quantum state collapses and is detected by the sender and receiver.
Most secrets like intelligence and nuclear launch codes are by way of symmetric encryption through keys shared by the sender and receiver which is secure but need physical exchange of keys. QKD can ensure its speedy distribution and be suited for national security communication.
Quantum Measurements
Just as picture requires light measurement and GPS needs time measurements, by using quantum principles of entanglement one can enhance and speed up these measurements. Quantum radars or LIDAR use pair of entangled quantum particles that make stronger co-relation and need fever emissions making detection stronger (like for detection of stealth aircraft). Since they use less power it makes it difficult for the enemy to detect and jam it. By using the entangled principles, disturbance in magnetic and gravitational fields can give greater information to detect underground bunkers and submarines and develop navigation system which do not require signals from GPS satellites and can, therefore, not be jammed.
The Impact on National Security
I. Information Security: Loss of Intelligence/ Disruption in Intelligence
Information security in all domains i.e. military, intelligence and business have implications for National Security. Decoding cryptography would be made easier by quantum computers. The fact that information can be downloaded now and decoded later would need investments in post quantum cryptography.
II. Military Use
A. Quantum Computations
Some of the Military/Security areas where quantum computation can be useful as drawn from various sources and research papers are:–
-
- Battlefield or War Fighting Simulations
- Radio frequency and satellite functioning
- Logistics Management
- Supply chain optimisation
- Energy Management
- Predictive Maintenance
- Autonomous and Robotic Vehicles/Stealth vehicles designing
- Medical Advancement and Emergency Response systems.
- Tracking space debris
- Predictive analytics and ML/AI in Military and security fields.
B. Other Military Uses
- Chemical and Biological Weapons simulation: Protein folding peptide research in biological warfare offence and defense, chemical weapons detection via quantum simulator and IED detection via a quantum cascade laser.
- New Materials: Materials new or old can be simulated by a quantum computer (as a quantum system) to improve specific designing for civil and military usages.
- Quantum Brain Mapping: (MEG/Magnetic Encephalography) or brain imaging for real time brain activity monitoring can be incorporated for designing soldiers helmet for remote medical monitoring and human machine interfacing.
- Space Warfare: By way of communicating satellites, satellite based quantum sensing, quantum space radars for object tracking, space based quantum electronic warfare can be given a new dimension.
- Underwater Warfare – Quantum communication uses blue green light which travel faster underwater than land. Quantum Lidar might allow submarines to detect underwater obstruction, mines, unmanned vehicles without giving away its own position.
- Electronic Warfare: Can be either quantum enhanced classical EW or quantum E-warfare for counter measures and support against quantum channels (used to transfer photons of quantum information). Quantum antennas, Quantum timing for Signal Intelligence (SIGINT) and Communication Intelligence (COMINT). Since quantum channels cannot be intercepted but disrupted it can also be used in future for denial of service attack.
- Intelligence, Surveillance Target Acquisition & Resonance (ISTAR):–
-
- Quantum computers and AI, ML can refine intelligence data for target identification.
- Quantum based sensing from land, sea, aerial vehicles, low orbit satellites.
- Quantum sensing for geo referencing, topographical mapping for mission planning in rugged terrain.
- Quantum 3D cameras with immense depth measuring capabilities can be used to explore mission destination resonance of hostile locations/installations.
- Quantum gas sensors to detect among other things chemical agents, human presence in the area.
- Quantum imaging for night vision devices and navigation.
- Quantum rangefinder with stealth features and quantum ghost imaging.
- Positional Navigation Timing Systems (PNT)
- Quantum based technology for PNT in difficult situations like in areas of GPS jamming, underwater and underground environment (via ground and satellite based atomic clocks, quantum gyroscopes and accelerometer). Although it will take time they will not readily be susceptible to jamming and electronic warfare.
- Quantum cyber security
-
- Post quantum cryptography usage to prevent data stealing, for security of Internet of Military things (IoMT) and to counter quantum attack capabilities
III. Quantum Drones
Efforts are on way to develop drone-based, mobile quantum network to seamlessly manoeuver around structures, nano-drones capable of chasing a human being through a multistory building, accurately navigate an area of ground to locate and then classify landmines, negotiate rough weather and terrain and quickly adapt to changing environments as in warfare.
According to research at the Air Force Research Laboratory (AFRL) Information Directorate, USA the combination of quantum communication and Unmanned Aerial Systems (UAS) represents an important advance in the Indian Air Force’s efforts to create field-able quantum systems for any war fighter, additionally, the potential of secure communication from a portable quantum communication UAS in contested environments represents important future capabilities for the Air Force.”
The drones could provide one-time crypto-keys to exchange critical information, which spies and enemies find difficult to intercept. Sooner or later one could incorporate quantum memory in the drones so that they can conduct error correction, relay and store information.
IV. Robotics and Quantum Technology
Concepts such as “Accelerated Warfare” and “Army in Motion” principles are linked to robotics and autonomous systems, artificial intelligence and quantum technologies. Robotics and manned-unmanned teaming is an emerging field. Robotics Autonomous System (RAS) concepts and technologies are gaining ground.
The RAS strategic aim is to maximise a soldier’s performance like improving decision making, generating mass and scalable effects (human-machine teaming and swarming technologies), force protection, and efficiency.
Response: Ready for Tomorrow?
A. The Securitisation Theory
The Securitisation Theory states that National Security Policy is not natural but designated by politicians and decision makers or as articulated by other ‘Securitisation actors’ mostly bureaucrats. The end user, the Military and Security agencies are now increasingly being consulted.
The routine task of cyber security would be more important and critical in the quantum world. Political leaders, policy makers all need to be sensitive to the opportunities and challenges in a quantum world so as to begin planning. Basic research and development along with partnership with institutes and private companies would be imperative so as to have an actor network quantum innovative ecosystem in place. Quantum needs to be integrated into strategic planning in the defense, intelligence and business fields so as to be mutually beneficial.
B. International Arena and China
Governments across the world have invested in quantum technology but China accounts for around 44 percent of total global central public funding. Chinese Universities and companies have filed more patents than the USA, EU, Japan and Korea combined. These technology demonstrators if successful can help nations leapfrog traditional military/security balance. In this regard China’s known civil military fusion policy may raise serious national and international security concern.
C. Civil-military-intelligence partnership
The scenario calls for a closer-civil-military-intelligence partnership in the development of quantum technologies within the framework of the actor-network theory.
India must also conduct a quantum security audit and develop international collaboration to counter any national security threats. Two observations would make the entire task difficult. First is the fact that although the Technology Readiness Levels (TRL’s) at present are low for these quantum technologies, their disruptive potential can be great. Secondly, with China as an adversary investing most heavily in these technologies and claiming unverifiable success any dispassionate exercise in this regard would not be an easy task.
D. Military / Intelligence Preparation: would need the following efforts
Quantum sensitisation of the military and the security agencies of the dual use technologies.
To have a rational audit of quantum workforce in the country and develop a “quantum ecosystem”.
Tracking of quantum technology evolution and adoption by various actors across the globe to avoid getting caught by quantum surprise “especially by any neighboring or hostile country.
To put in place policies and strategies so as to respond to the strategic ambition of adversaries.
The governments to consult consider and incorporate the military / intelligence views in the overall national “quantum strategies”.
Military and Intelligence to develop a realistic and pragmatic time line and road map which would reflect a practical investment of time and reserves.
The academic practitioner model of involving universities/institutions/companies to be followed from the very beginning including involving startups who can come up with disruptive ideas.
Summary
Quantum technologies are, therefore, a part of part of a group of promising disruptive technologies that have the potential to disrupt may of the activities in the military and intelligence domains critical for National Security. They are not a single but diverse, complex technologies with low level of technical readiness, in terms of their application at present. We should think in new ways both to exploit these both for offence and defense. The challenge will be to adapt them in a cost effective manner through a proper allocation of resources and not be caught by a ‘Quantum surprise’ in future.